203 billion euros per year in Germany alone – that’s the damage caused by hacking cybercrime attacks, as estimated by a study conducted by the digital association Bitkom. That’s immense and it can seriously threaten a company’s existence in seconds. Experts estimate an average loss of four million euros per incident. It’s clear that companies’ old IT security concepts urgently need to be reviewed in traditional IT environments as well as online shops and cloud-based applications.
Today, economic success depends on digital networking with business partners. This inevitably creates more and more interfaces and thus, greater targets for cyberattacks. The threat situation on the Internet is continuously growing and affects different areas of business and tools. Cybercrime is now more professionally organized than ever before. Attackers use a business model called “cybercrime as a service,” where they don’t even have to develop ransomware, hacking tools, or phishing kits themselves. They can simply rent or buy them, just like regular software solutions. This simplifies access to sophisticated attack techniques, so less tech-savvy perpetrators can carry out attacks.
Cybercriminals are increasingly targeting SaaS business applications with the help of AI tools and deceptively realistic phishing campaigns to obtain access data. In reality, it can look like a seemingly legitimate internal message being sent, for example, on behalf of the IT department. The goal of these attacks is to trick employees into revealing their passwords. These gateways often lead to major security incidents with serious consequences. A successful phishing attack can give cybercriminals access to sensitive company data, which can lead to data theft, financial losses, and even business interruptions.
Although modern cloud platforms have robust protection mechanisms, attackers are also very familiar with them. They use targeted methods to exploit misconfigurations, insecure APIs, and inadequate access controls. Companies shouldn’t just rely on the standard security measures their cloud providers offer. They should also actively integrate cloud security tools into their protection strategy and arm themselves against new and increasingly creative threats.
Let’s take a look at a cyberattack on the British company Marks & Spencer. It became public in April 2025 and cost the fashion and food retailer dearly. The loss of online business alone, which lasted several months, resulted in financial losses of around £300 million (more than €400 million) in operating business, according to a company announcement. M&S shares lost around 3 percent on the London Stock Exchange – an estimated loss in value of more than £200 million. Add onto this considerable damage done to the company’s image and reputation, as personal customer data was stolen.
Three days after the attack was publicized, the company had to stop accepting clothing and home textile orders on its website and app, but by then it was already too late: the impact of the hacker attack on all areas of the company was immense. Stores had to resort to manual processes, using pen and paper in the “old-fashioned” way, logistics costs rose, and food became scarce in some cases. The attack route was manipulated login credentials at a help desk service provider – a classic application security gap (ASG).
Where does the application security gap come from?
Indeed, this is where the main problem lies. Most entrepreneurs feel protected and have never heard of an application security gap. Basically, this significant gap in security configuration and monitoring arises from the problem of responsibility and often goes unrecognized. An in-house IT department can monitor internal processes, but not a cloud-based customer portal or online store. In turn, cloud providers monitor their infrastructure, but not the application connecting them to the company’s internal processes and databases. This creates a security gap: the application security gap. Since most companies now use cloud-based applications, they’re exposed to this potential danger, a digital flank through which attackers can gain access.
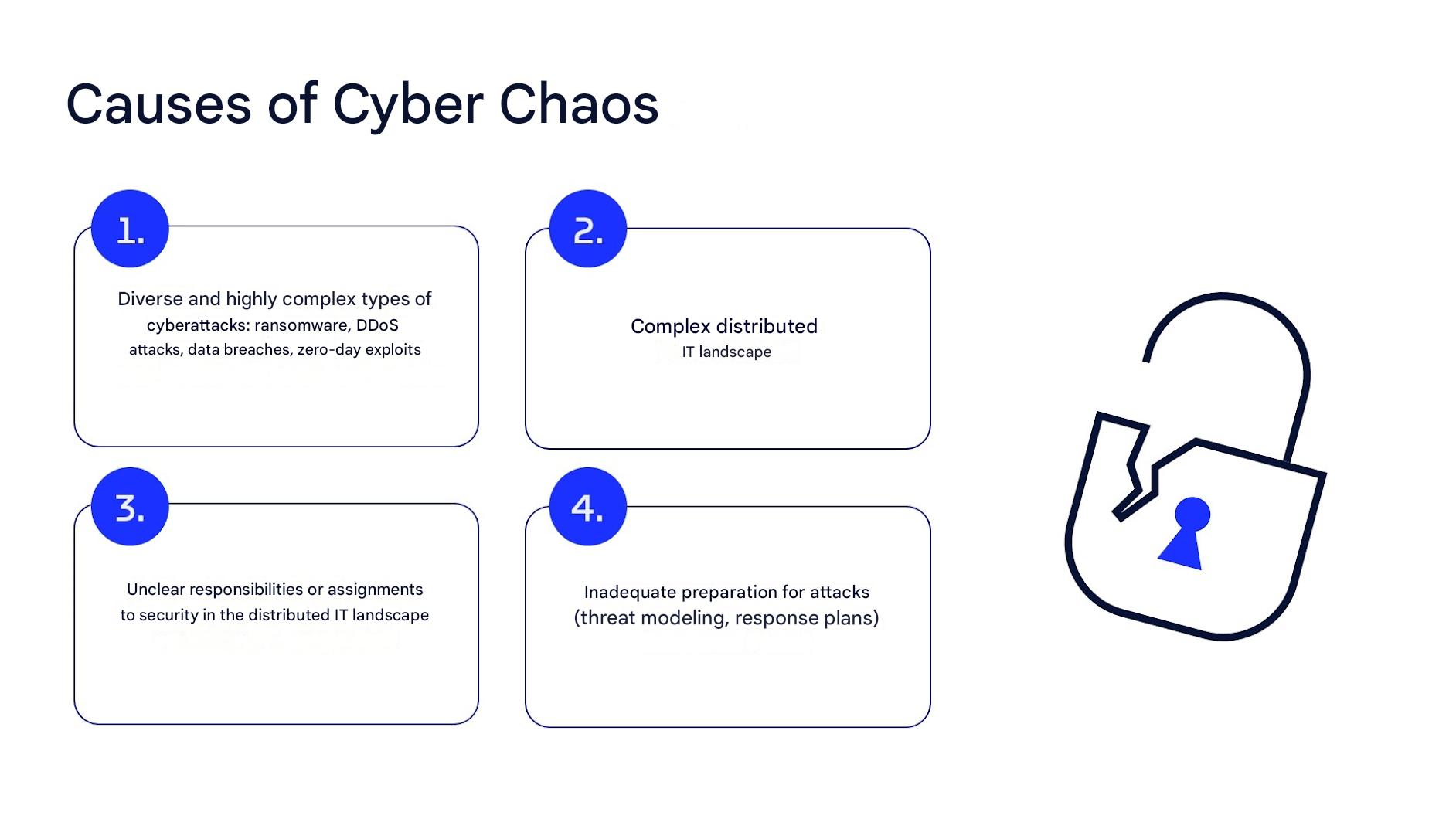
Fig. 1: What constitutes the security gap
Applications and cloud applications are attractive to attackers for several reasons:
- They’re directly accessible over the Internet.
- They use cloud platforms and technologies that attackers are also very familiar with.
- They often contain personal or internal company data.
A thorough inventory and analysis can provide insight into the most urgent need for action. Fundamentally, the questions that arise in this context are: Am I aware of the threats to which my application is exposed? Do I understand and use the security features of the cloud platform correctly? If you decide on a cloud solution together with your IT service provider and your company’s internal IT department, you should be aware of the risks and dangers and take appropriate precautions.
Distributed responsibilities: Risky, but necessary
In IT landscapes, there’s often a strict division of labor between development, operations, infrastructure, and security. This has its benefits, as it increases efficiency and takes technical specializations into account. But on the other hand, it often leads to unclear responsibilities. This is especially a problem in cloud-native applications. The infrastructure is monitored by the provider, the business logic lies with the developers, and monitoring – if it exists at all – often focuses on technical metrics like CPU utilization or availability, but not on security-related aspects.
The application security gap is so treacherous because it arises in areas where security responsibility is unclear and it cannot be reliably detected by traditional firewalls or standard intrusion detection systems. Many IT managers rely on certified cloud infrastructure and fail to recognize that application security is explicitly not part of many cloud service level agreements. The combined lack of knowledge about the ASG, distributed responsibilities among several people, and lack of security measures in the DevOps pipeline is particularly dangerous. The latter refers to an absence or inadequate implementation of security mechanisms throughout the software development lifecycle, especially in automated continuous integration/continuous deployment (CI/CD) pipelines typical in DevOps processes.
In detail, this means that in modern DevOps environments, software is continuously built, tested, and delivered. If security aspects aren’t integrated in this process, considerable risks arise. Above all, missing or insufficient security monitoring and errors in the system architecture’s security configuration are the two most obvious application security gap characteristics. Specific examples of these two aspects include:
- Brute force attacks on the application are not detected or reported by the system.
- Multi-factor authentication (MFA) is not used correctly or comprehensively for administrative access.
Typical missing security measures in development and CI
- No static code analysis (SAST): No automated checks are performed for security vulnerabilities in the source code (e.g., SQL injection, XSS, hard-coded secrets).
- No dynamic testing (DAST): Web applications are not tested for attack vectors while running.
- Lack of dependency checks (SCA): Libraries and frameworks are not checked for known vulnerabilities (e.g., via OWASP Dependency Check or GitHub Security Alerts).
- Secrets in plain text: API keys, tokens, and passwords are stored unprotected in the code, in build scripts, or in environment variables.
- No access controls on CI/CD systems: Build systems such as Jenkins, GitLab CI, and GitHub Actions are not secured or have excessive permissions.
- Missing security gates: Security issues do not automatically block builds, therefore insecure artifacts make it into production.
- Untested artifacts: Container images or packages are pulled from untrusted repositories without signing or testing.
- No auditability/logging: CI/CD processes are not traceable, no logs or monitoring by security information and event management (SIEM) systems.
Cloud solutions: Advantages and side effects
The fact is that cloud computing has had a strong upswing in recent years. More companies are outsourcing services, infrastructure, and applications to the cloud to accelerate digitization, scale flexibly, and reduce operating costs. Many features ensure that cloud solutions are a “well-rounded affair.” In fact, studies show that around 45 percent of all companies in the EU use cloud services for standard applications including email, file storage, and office applications. Over 75 percent outsource security or database-related services.
Cloud solutions provide lean IT structures, cost efficiency, maximum flexibility, and speed of innovation in most industries and companies thanks to their high scalability in response to changing requirements and conditions. Cloud services offer a high degree of automation and global accessibility, giving them real advantages over other solutions. However, cybercriminals are also aware of cloud services and their configuration options.
Potential security problems usually don’t lie in the cloud itself, but primarily in how it’s used. Many companies simply underestimate the attack surfaces that cloud solutions open up for hackers. Cloud providers have a shared responsibility model with global reach and enormous network resources (hyperscalers) that make it clear that application security is entirely the customer’s responsibility. Risks for companies can be very high.
- Cyberattacks and misconfigurations: Several cloud migrations have already led to security problems due to inadequate API protection, incorrectly set permissions, and SQL injection attacks. This can result in a highly dangerous cyber threat matrix, including account takeovers and data exfiltration.
- Dependencies on the provider: When critical services (e.g., identity and access management) are managed by the cloud provider, responsibility shifts. The cloud provider controls if there is a security backdoor or if updates are installed on time.
- Unforeseen costs: Improper resource management quickly leads to budget overruns. It’s not uncommon for cloud services running for several years to exceed the originally planned on-premise costs. Many organizations fail to optimize their resources.
- Jurisdiction and data sovereignty: In a globally distributed cloud, it’s often unclear where data is ultimately stored. If a provider stores data in another country, different legal frameworks apply. This can be a problem for international corporations in terms of law enforcement, compliance, and data protection.
However, although non-cloud-based in-house solutions may seem like a secure alternative in light of these risks, don’t be fooled. Most in-house solutions cannot match cloud service capabilities in terms of timeliness, security tools, and monitoring mechanisms.
Large cloud providers have high security standards with many up-to-date tools that companies should use – often in a confusing array. Regular updates offer good basic protection and they can adapt to current risks and threats. A company’s own security remains an internal manner that its IT managers must take care of, but the tools on offer are a worthwhile investment. Yet, this point is often neglected because their secure use requires a great deal of knowledge and organization. And so, it’s come to the point where application security gaps arise.
Digression: Shadow IT, the silent threat
In many organizations a different security risk arises in a completely different place than you might expect: among employees. This is where we encounter the term “shadow IT.” It refers to all IT systems, cloud services, software tools, and devices that employees use in a company without them having been approved by the IT department or management. Shadow IT usually comes from good intentions, like speeding up processes, circumventing complex approval procedures, or adapting workflows for individual requirements.
The desire for greater efficiency, flexibility, and speed is understandable, but the risks outweigh the benefits. A seemingly harmless, unauthorized download that the internal IT department is unaware of can quickly lead to financially and legally risky situations. Security gaps that arise aren’t detected in time because of a lack of monitoring. Shadow IT isn’t just a problem from a security perspective. It has numerous other risks.
Security risks
Many security risks arise, including:
- Increased attack surface: Unauthorized cloud apps operate outside the company firewall and often don’t use multi-factor authentication systems – ideal gateways for attacks.
- Data loss: Unauthorized tools store sensitive data outside secure environments.
- Integration without control: Shadow IT tools can be introduced into existing systems without testing, for example via unsecured APIs, causing critical security gaps.
- Lack of verification: If there is no integration with monitoring, logging, or SIEM, attack windows remain undetected for a long time. No one knows the code or monitors the tool.
Compliance violations
Compliance violations can quickly occur:
- Copyright and licensing issues: Tools are often installed without the correct license. Software manufacturers can demand cessation, damages, or expensive retroactive licenses.
- GDPR and NIS2: Uncontrolled data processing outside of approved platforms risks data protection violations, with fines of up to four percent of the annual revenue.
- Audit compliance and audits: Without a complete audit trail, organizations lose track of things – a classic violation that can lead to severe penalties.
Financial damage and inefficiency
Shadow IT also leads to inefficiency and potential financial damage:
- Duplicate spending: Teams might subscribe to the same SaaS solution multiple times, often at more expensive rates without volume discounts.
- Loss of unused licenses: Automatically renewing unneeded services that are used without the IT department’s knowledge creates unnecessary costs.
- Waste of time and resources: IT teams have to provide unexpected support for unknown tools. Employees spend time using tools instead of collaborating.
Lack of control and governance
Lastly, shadow IT eludes control and governance, which leads to problems:
- Lack of overview: IT departments experience transparency blackouts. In one example, instead of an estimated 20 to 30 tools, around 1,300 unknown applications were discovered on the network. Many of these had serious security vulnerabilities.
- Version and update chaos: Shadow IT tools are rarely patched or updated regularly, so existing security vulnerabilities cannot be closed in a timely manner.
A holistic approach is essential to effectively manage these risks. Organizations need clear guidelines, technical visibility tools, training, and structured license management. This is the only way to ensure long term transparency, compliance, and security for corporate IT:
- Regular shadow IT audits: Use tools like Cloud Access Security Broker (CASB) to discover new services.
- Approval requirement: New creations must be requested centrally and checked against security parameters.
- Training for specialist departments: Raise awareness of structural risks.
- Offer security goodies: Provide central templates, APIs, and PaaS building blocks to avoid shadow IT from the outset.
Digression: Legal frameworks for GDPR, NIS2, and more
The new EU NIS2 directive requires companies from 18 sectors—including IT service providers, digital platforms, and cloud providers—to implement significantly more comprehensive security measures. The scope of application has been greatly expanded: Companies with 50 or more employees or ten million euros in revenue are subject to the regulation. The core requirements include:
- Risk management systems (including supply chain)
- Incident response processes
- Regular security audits
- Training requirements
- Mandatory reporting of serious security incidents within 24 hours
GDPR and application security
Security gaps are also relevant in terms of data protection law, especially for applications that process personal data:
- Unauthorized access = reportable incident
- Inadequate protective measures = risk of fines
- “Privacy by Design” is mandatory
Other relevant standards and frameworks
- ISO/IEC 27001 and 27017 for cloud security
- BSI Basic Protection Compendium
- OWASP ASVS for web application security
Solution approaches: From problem to structured strategy
This raises the question: what specific measures should companies take when it comes to application security? Almost every organization needs to take action in the short term. But it’s important to realize that not every vulnerability can be fixed immediately; priorities must be set.
One thing is clear: cybersecurity only works with shared responsibilities. This is especially true in modern corporate IT landscapes, where numerous applications and tools are used on a wide variety of platforms. Anyone introducing a business-critical application must understand and define who is responsible for that application’s security. Security measured based on this responsibility can be effectively established for each application.
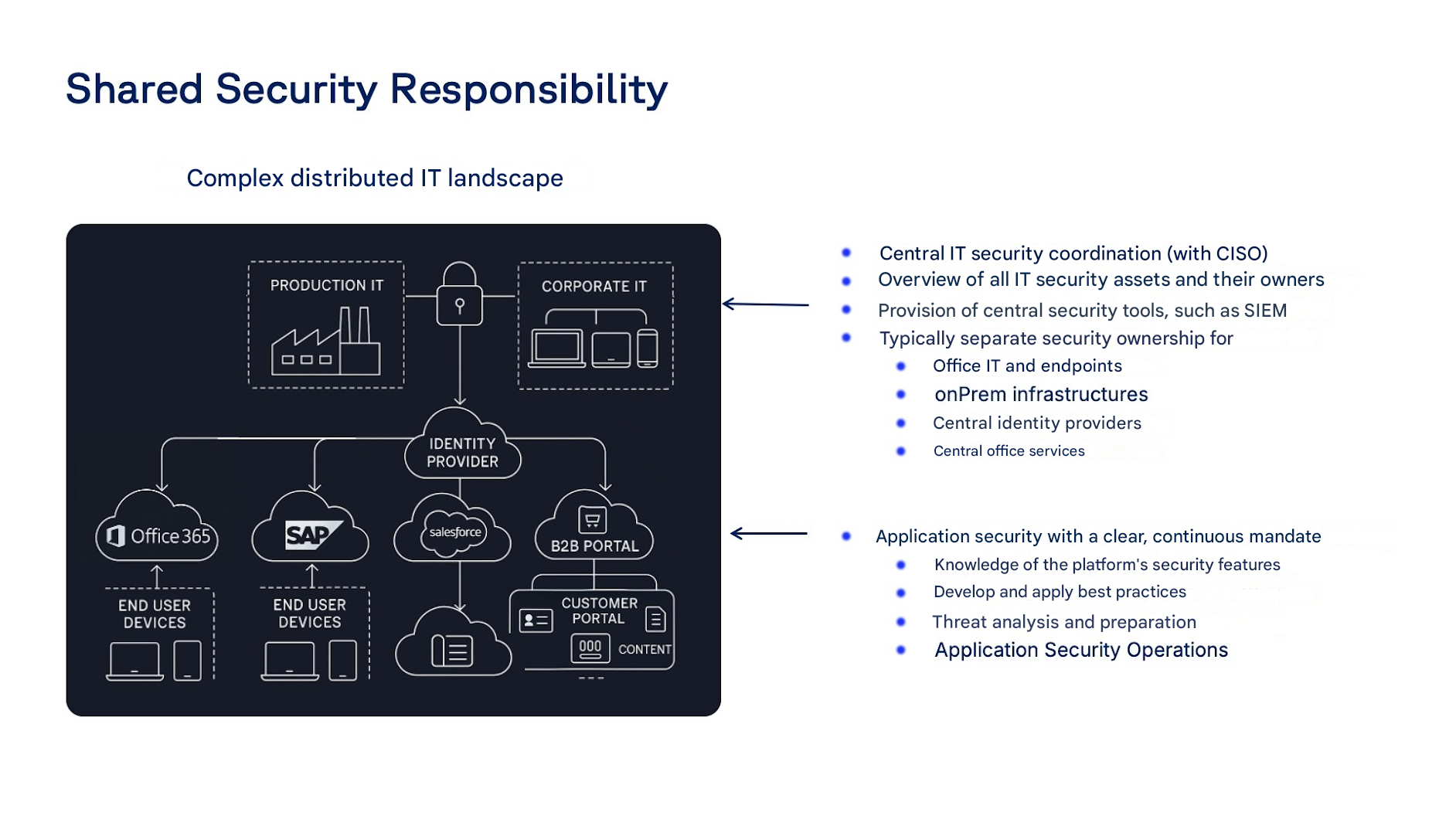
Fig. 2: Shared security responsibility
Immediate measures
Every application owner should first conduct a comprehensive security analysis to identify the biggest vulnerabilities. This includes security checks and threat analyses showing where criminals could strike. Specifically, this means:
- *Tailored security reviews: These ensure that the best security practices for the platform, frameworks, and technologies are correctly established and used. This includes many aspects, including MFA (multi-factor authentication) settings in platforms and clouds, REST API security with OAuth and CORS, security headers in web front ends, k8s security scans with Kubescape, etc.
- Threat modeling for the entire application landscape: The STRIDE analysis method is used to determine in which data flows threats from the STRIDE categories exist (spoofing, tampering, repudiation, information disclosure, denial of service, elevation of privilege). The DREAD (Damage, Reproducibility, Exploitability, Affected Users, Discoverability) analysis method is used to determine which risk class the respective threat is assigned to.
Short-term measures
Identified risks should be prioritized and the most important vulnerabilities should be quickly remedied. This closes potential gateways for cybercriminals and helps detect attacks quickly. This means:
- Risky vulnerabilities that can be fixed by code and configuration changes should be prioritized and quickly eliminated.
- Other threats should be addressed through targeted security alerts. These “tripwires” make attempted attacks or anomalies visible immediately, and if necessary, further manual analysis is initiated. Security alerts should be set up step-by-step in a professional SIEM (Security Information and Event Management) tool and form the basis for real security operations.
Medium-term measures
Security operations should be continuously established and expanded for each application, both in terms of tools and personnel. Specifically:
- The security monitoring framework must be continuously expanded and optimized so that current threats can also be detected.
- Automating responses enables a SecOps team to react quickly and effectively in the event of an attack. In the case of cyberattacks, quick action can prevent a large part of the damage.
With a professional SIEM and SOAR (Security Orchestration, Automation, and Response) tool and built-in security dashboards and alerts, a Security Operations Center (SOC) can work effectively, ensure the greatest possible application security, and permanently counter the growing risks of cybersecurity amidst constant change and attack improvements. Companies can staff the SOC themselves or hire a service provider to do so. Outsourcing these services lets even small and medium-sized companies finance the highest level of security.
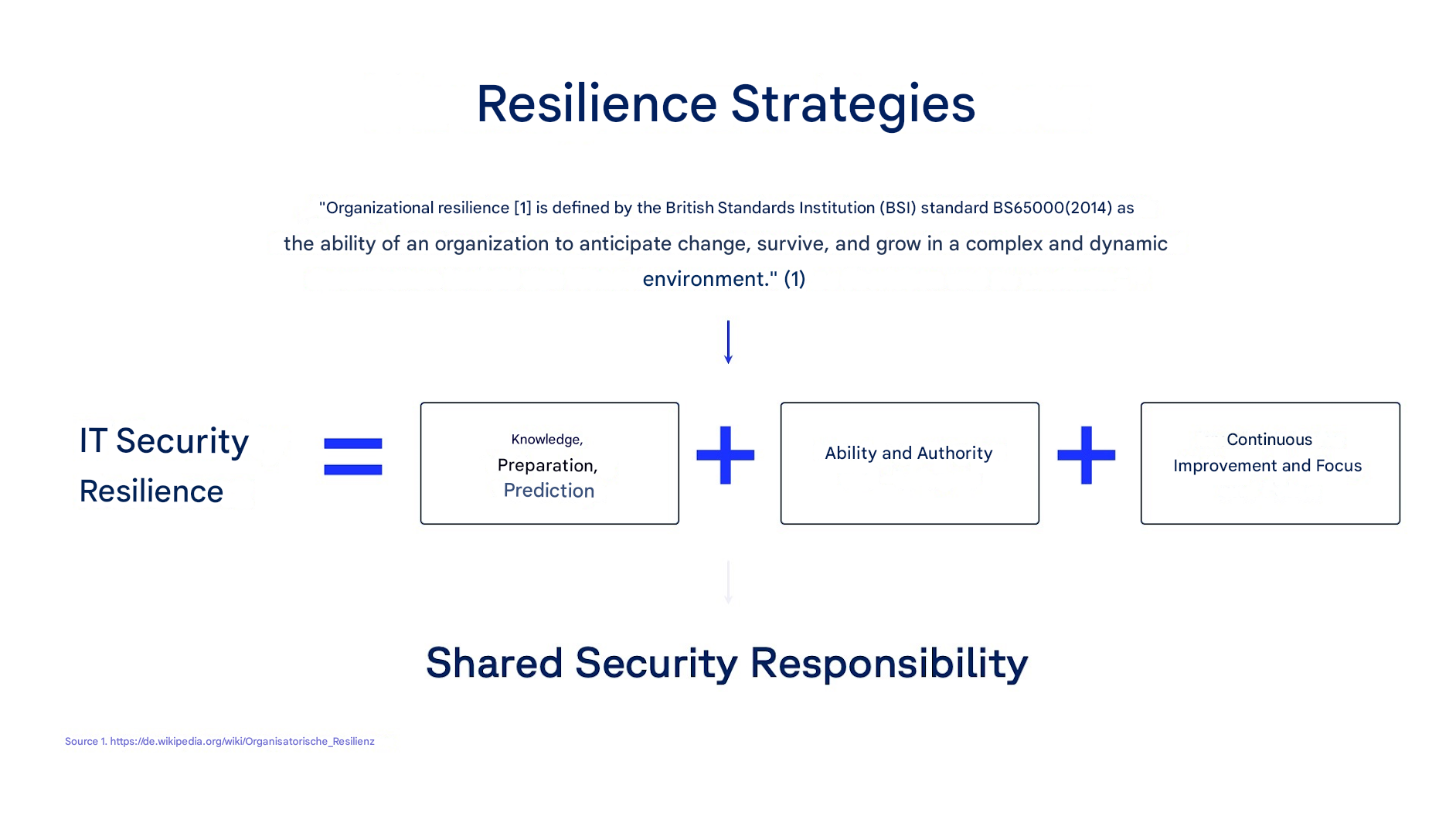
Fig. 3: Resilience strategies
Conclusion: The application security gap is manageable
The application security gap and cloud solution risk are structural weaknesses that should not be underestimated, but they are not inevitable. If they are identified, addressed, and systematically tackled, the growing threat of cyberattacks can be effectively contained. The decisive factor is not the size of the company, but the awareness that applications and cloud solutions are now the primary level of attack – and must be at the center of any IT security strategy. The fundamental problem of responsibility and the gap between cloud providers and companies must be addressed. Employees should be involved and made aware of issues concerning shadow IT and granting access rights, for example, to documents stored in the cloud.
There is no such thing as absolute security. That would be an illusion given today’s highly heterogeneous IT infrastructures and complex environments. However, those who focus their attention on this issue, use the tools offered by SaaS providers in a targeted and considered manner, and implement a tailor-made, individual solution for their own organization are operating within a secure framework.
What can companies do to build a robust security strategy? Create transparency, monitor threats, and respond flexibly. An important principle is that cybersecurity is a team sport – it only works when all departments work together.
Checklist: How secure is my company?
☑ Do IT risk assessments take the application security gap taken into account?
☑ Is application security systematically and independently checked?
☑ Is there a central register of all web applications and APIs used?
☑ Are responsibilities for applications and their security clearly defined?
☑ Are security tools (SAST, DAST, SCA) integrated into the CI/CD pipeline?
☑ Is there a reporting chain for security incidents in accordance with NIS2 and GDPR?
About the cybersecurity audit: https://www.diva-e.com/de/services/ams/cybersecurity
Author
🔍 FAQ
1. What is an application security gap?
An application security gap is a hidden weakness or blind spot in an application’s security controls that attackers can exploit. These gaps often arise from misconfigurations, insecure code, or lack of visibility across systems.
2. Why are application security gaps considered “invisible”?
They are called “invisible” because they often exist outside traditional security monitoring tools—especially in complex cloud, SaaS, and API-driven environments—making them difficult to detect until exploited.
3. Why do traditional security approaches fail to detect these gaps?
Traditional security focuses on networks and infrastructure, but modern applications operate across cloud services, APIs, and third-party integrations—creating blind spots that legacy tools often miss.
4. What role do APIs play in application security gaps?
APIs expand the attack surface and are frequently targeted due to weak authentication, poor monitoring, or misconfigurations, making them a major source of security gaps.